Showing posts with label academic. Show all posts
Showing posts with label academic. Show all posts
Saturday, 14 February 2026
A research article’s digital cul-de-sac. How to fix an academic paper that is hidden and/or unreachable
Written for researchers keen to understand potential obstacles to their articles not being readily searchable via academic indexes and search engines thanks to broken linkages, a metadata mismatch or non-submission. Updated- 22 March 2026
Most researchers are keen for their works to be well-indexed, quick-to-find, and reliably linked to their academic publisher’s landing page from search engine results. This is especially true for scholars whose performance reviews include consideration of their works’ impact in reaching interested readers. Such impact scores can include citations, amplification and readership, as tracked via altmetrics and other sources.
However, each author was unable to select this listing for automatic addition, despite entering the assigned DOI index number, the full handle.net address (Figure 10) or the journal's URL.
Instead, I shared a screenshot of the details I used (Figure 11) which each author copied for adding the same details.
The primary responsibility for submitting and maintaining Crossref entries typically lies with the publisher in being formal Crossref members. CRIMSA publishes Acta Criminologica : African Journal of Criminology & Victimology. The editor ensures that high-quality metadata (such as ORCIDs and funding info) is received from authors before manuscript approval. CRIMSA would then be responsible for submitting accepted articles' bibliographic metadata (including URLs and references, plus registering DOIs), then ensuring this information remains up-to-date. The publisher handles the technical side of generating "Crossref XML" files, or using deposit tools.
If there is a problem, it is most likely to be taking place in the earliest phase of the Research Data Lifecycle (RDLC)- this broad concept is used to describe the "cradle-to-grave" journey of research data:
However, until this happens, authors keen to share their Acta Criminologica publications via their scholarly profiles and social networks must do a lot of extra work. My colleagues and I followed work-arounds to address the placeholder DOI index information in phases 2 to 4. These included listing their article's and/or handle.net address in manual entries on ORCID's centralised registry, academic aggregators (e.g. Google Scholar or Bielefeld Academic Search Engine). Plus, shifting to using the handle.net address in academic social network posts. These work-arounds required extra labour from the four authors, three of whom are independent and not formally affiliated to any university. As the journal publisher already covers the journal's Crossref fees, such extra work can readily be avoided. Hopefully, the journal will put aside the resources necessary for generating the required XML metadata, and for depositing its full archive, plus new publications via Crossref's record manager.
N.B. Kindly add a comment below if you have any related suggestions or other feedback...
Most researchers are keen for their works to be well-indexed, quick-to-find, and reliably linked to their academic publisher’s landing page from search engine results. This is especially true for scholars whose performance reviews include consideration of their works’ impact in reaching interested readers. Such impact scores can include citations, amplification and readership, as tracked via altmetrics and other sources.
This post provides an example to illustrate why a research author should not assume that every article of theirs will be properly indexed. As result, this work may not be seen by potentially interested parties searching for pertinent work with salient keywords, despite the work's merits. Metadata mismatches and broken linkages can unwittingly emerge during academic publishing, and may persist if not checked, flagged, and corrected. This post gives helpful advice for correcting or working around a few key problems. It shares the practical example of errors that impacted a South African journal article's availability after its digital publication on the 1st of December, 2025:
'Brandjacked for social media advert fraud'- a ghost in the fog...
The first publication from a research project that began in 2021, Brandjacked for social media advert fraud: Microcelebrities' experiences of digital crime, was published in the Acta Criminologica: African Journal of Criminology & Victimology journal. Ordinarily, new articles should only take a few weeks after being indexed by an an academic metadata aggregator, such as Crossref, before featuring on authors' academic profiles. Crossref can update researchers' ORCID and Google Scholar records, followed by listings on academic social networks. These may be preceded by results in search engines and in Artificial Intelligence results (such as Grok). While search results for Brandjacked were quickly available from the last two, it could not be found under any of the former by February, 2026.
This post explores such challenges, the root cause of the article not being be properly indexed for academic searches, plus the work-arounds that Brandjacked's authors followed. While their paper technically existed, it could not efficiently be shared online by the four co-authors, with some listing results defaulting to a 'page not found' error message, rather than the publisher's article landing page:
Multiple URLs as expected
A normal part of the academic publishing process sees several URLs being created for a particular publication. In Brandjacked's case, these are from the handle.net domain (pointing to hdl.handle.net/10520/ejc-crim_v38_n3_a2) and journals.co.za's (onto journals.co.za/doi/10.10520/ejc-crim_v38_n3_a2). Sabinet African Journals (journals.co.za) is a searchable platform providing a comprehensive, full-text collection for over 600 African-published electronic journals. Handle.net is developed by the Corporation for National Research Initiatives (CNRI) to support a distributed information system for persistent, unique, and actionable identifiers (handles) for digital objects over the internet. The Handle System is the underlying technology used by the Digital Object Identifier (DOI) setup for identifying content, particularly for digital publishing and commerce.
Brandjacked's DOI value changed post-publication
A DOI is a unique, permanent alphanumeric string that is assigned to digital objects. DOIs include a prefix always starting with 10 and a suffix, separated by a forward slash (/). Prefacing the DOI with doi.org creates an actionable link. Originally, the Brandjacked article was allocated the DOI 10.10520/ejc-crim_v2025_nse1_a2. However, this was subsequently changed to 10.10520/ejc-crim_v38_n3_a2 to reflect the article’s publication as the second in the 38th volume’s third issue. Commonly linked to journal articles, books, and research datasets, each DOI should provide a stable, long-lasting link to a research output’s internet location, regardless of whether its online address [or Uniform Research Location (URL)] gets changed.
Social media shares…
On social media, academics, researchers and scholars typically share the DOI version of URLs, since a DOI's usage is the primary identifier for tracking comments and mentions via altmetrics. Attention for academic publications is typically sparse, with most not being shared via social media, and a significant portion only being shared once via popular platforms. Only a few papers, often with high public interest or "quirky" topics, receive the vast majority of shares. To help Brandjacked's visibility, I wrote a 31 tweet long thread at x.com/travisnoakes/status/2001585342000898177, shared a LinkedIn post at linkedin.com/feed/update/urn:li:activity:7407406366052569089/, and wrote this public Facebook post at facebook.com/share/p/1BtsXaJtQC/.
… but no AltMetrics listing yet
On the Brandjacked article’s landing page, the altmetrics badge only shows a question mark at the date of this post's publication (see Figure 1 below).
 |
| Figure 1. Screenshot of No AltMetrics listing for Brandjacked article,12 Feb 2026. |
Nor are results for the Brandjacked article shown on app.dimensions.ai/discover/publication?search_mode (see Figure 2).
 | |
|
As a research blogger, I like to share Altmetrics badges for my publications, but none is available for Brandjacked via badge.dimensions.ai/details/doi/10.10520/ejc-crim_v38_n3_a2?domain=https://journals.co.za. Nor for a PlumX badge, searching with Branjacked's DOI value at https://plu.mx/plum/a/?doi=10.10520/ejc-crim_v38_n3_a2.
No automatic ORCID profile article update
Each of Brandjacked’s four authors have an Open Researcher and Contributor ID (ORCID) address. This is a 16-digit persistent digital identifier (e.g., 0000-0001-9566-8983) that uniquely identifies research-contributors all over the world. Like the DOI value does for research outputs, ORCID resolves name ambiguity. It links all research publications, datasets, and grants to an individual, regardless if their name or institution changes. Authors can set their ORCID profile to be automatically updated with research outputs that are linked to them. As at this post’s publication date, the Brandjacked article had not automatically been linked to any of its authors’ ORCID profiles.
Google Scholar links to a 404 error
The academic search engine, Google Scholar, is popular due to offering the widest automatic global indexing of scholars' works. Its account holders can create manual entries for their research outputs, or select pre-existing records featuring their author name. In Brandjacked’s case, I created a manual record in late December, since no record for this paper was available for selection (Figure 3). Since then, Google Scholar has come to list two versions of the article.
 |
| Figure 3.Screenshot of Two versions of Brandjacked on Google Scholar, 12 Feb 2026. |
The top version, which can be Saved and Cited, produced a '404 not found' error when clicked through to Acta Criminologica (Figure 4).
 |
| Figure 4.Screenshot of DOI not resolved from Google Scholar, 12 Feb 2026. |
Thinking that this may have been caused by the manual record I created featuring the initial DOI, I chose to delete the article from my record. Then went into Google Scholar trash and selected ‘Delete Forever’. However, the article available for manual selection (Figure 5) still links to a '404 not found' result.
 |
| Figure 5. Screenshot of Google Scholar manual selection of Brandjacked, 12 Feb 2026. |
Report a failed DOI link via doi.org
A manual entry created on ResearchGate (at researchgate.net/publication/398814505_Brandjacked_for_social_media_advert_fraud_Microcelebrities'_experiences_of_digital_crime_in_South_Africa) lists the correct DOI (Figure 6), but it also showed a '404 not found' error when attempting to link to the digital publication.
 |
| Figure 6.Screenshot of ResearchGate DOI being correct for Brandjacked, 12 Feb 2026. |
At least this page presented an option to report the failed DOI. So, I submitted this error report to DOI: "The article 'Brandjacked for social media advert fraud' should be available at this DOI. Related working URLs are: https://journals.co.za/doi/10.10520/ejc-crim_v38_n3_a2 & https://hdl.handle.net/10520/ejc-crim_v38_n3_a2. Thanks in advance for fixing this."
 |
| Figure 7. Screenshot of DOI error report for Brandjacked, 12 Feb 2026. |
As a shortcut for checking-and-reporting DOI errors, authors should open www.doi.org, then scroll down to the 'Try resolving a DOI name' section. There they can enter a DOI value to check it, and report a DOI URL address that fails in throwing a '404 not found' error.
![DOI Prefix [10.10520] Not Found.png DOI Prefix [10.10520] Not Found.png](https://blogger.googleusercontent.com/img/b/R29vZ2xl/AVvXsEjDEzqL4beKD8zMIGkhp6iWGUj-JBn6HNu5Kxiuk7YzppaCG5je4xEOMY0xNKm7XroYFTLduiyNrxPPZprQV-PDNvHlEmgVh5_aY4jmLe47-YFoi1U09UxXqurCEexdlvbO6fPvuf-BQ5T4CPmPYtfHufuU5oqAXWrvsZyzt5Tl5uQim1lw1W7pTg-qI1sq/w400-h235/DOI%20Prefix%2010.10520%20Not%20Found.png) |
| Figure 8. Screenshot showing DOI Prefix 10.10520 Not Found error message, 12 Feb 2026. |
Just a few downloads...
Acta Criminologica’s ‘Open Access’ policy initially provides restricted access via the South African Bibliographic and Information Network (SABINET)'s archives. These are available via university libraries’ annual SABINET subscription for SABINET African Electronic Publications (SA_ePublications). There is a 12-month open access embargo from the date of publication/loading on the Criminological Society of Africa (CRIMSA)’s website.
Perhaps being published before the Christmas holidays in an access-restricted versus open-journal format contributed to Brandjacked only being downloaded five times in the first two months. But even achieving that readership is not been helped by a ghost-listing amidst a heavy stream of academic publications. As Trend MD reports, nearly 8,000 research articles are published each day. In this flood of information, the visibility of our niche publication is hampered through not being indexed in aggregators for academic (meta-)data or authorial content registries. Consequently, it is vital for scholars to work with the journal, their publisher, and co-authors to achieve work-arounds. Authors should also build awareness around remedying any root causes that undermine their visibility of their academic work.
Emailed the editor
Given that the landing page URL is throwing a '404 not found' error and the DOI is not resolving, it seemed likely that the error was a flaw on the publisher's end. In response, I wrote to the journal's editor requesting that the Crossref metadata be updated. I hoped that the journal’s production team could soon ensure that: (i) the landing page URL for the article is correctly mapped to its DOI. And that (ii) the metadata provided to Crossref and other aggregators could be updated to reflect a functional DOI link. As this issue impacted other articles in the Cybercrime special issue, it seemed crucial to fix for the visibility of all its authors’ articles.
Subsequent investigation spotlighted that the failure for the DOI to resolve actually applied to all articles in the journal: prior to 2017, the 'Acta Criminologica: African Journal of Criminology & Victimology' journal was known as 'Acta Criminologica: Southern African Journal of Criminology'. Its first issue started in 1988, and entering its first ever article's DOI produces exactly the same error as shown in Figure 8.
Feedback from the publisher
A product manager for content services at SABINET replied to the editor's query that the DOI link is not working as the journal is not using registered DOIs yet. The 10.10520 prefix is a "dummy" DOI that SABINET uses to ingest content. By contrast, the persistent link to resolve each article is at a fully-functioning https://hdl.handle.net address.
The product manager offered to reach out to the Google Scholar team to ask that they use the handle link rather than the DOI code, unless they use the complete URL. She also flagged that the DOI issue can only be addressed for future Acta Criminologica articles once their allocated actual DOIs are registered with Crossref. This issue relates to a broader problem around the visibility of African journals that Asubiaro and Onaolapo (2023) have spotlighted- their 'low representation in Crossref, a free indexing infrastructure that could be harnessed for building an African‐centric research indexing database, is concerning'. This paper flags how less than fifty percent of journals from Africa feature in Crossref.
Not being indexed there has an important knock-on effect, as it provides data for other bibliographic databases. These include Dimensions, The Lens and Scilit. In the Lens' case, it serves global scholarly records. These are compiled and harmonised from Crossref and PubMed, enhanced with OpenAlex and UnPaywall open access information, CORE full text and links to ORCID. Data from The Lens can be imported into ORCID records, allowing authors to synchronise their records.
A manual ORCID listing
In the absence of such synchronisation for Brandjacked, I could not select a DOI or handle.net address in ORCID for automatically linking to my record. Instead, I created a manual one. Its entry route provided an option to define both the DOI's 'identifier value' (10520/ejc-crim_v38_n3_a2) and the full identifier URL's address (https://hdl.handle.net/10520/ejc-crim_v38_n3_a2) (Figure 9). I asked my co-authors to add this manuscript to their ORCID records, which correctly resolves to the publisher's article landing page.
 |
| Figure 9. Screenshot of applying the handle.net identified in manual ORCID listing, 16 Feb 2026. |
However, each author was unable to select this listing for automatic addition, despite entering the assigned DOI index number, the full handle.net address (Figure 10) or the journal's URL.
 |
| Figure 10. Screenshot showing handle.net URL does not work for co-author selection via ORCID, 16 Feb 2026. |
Instead, I shared a screenshot of the details I used (Figure 11) which each author copied for adding the same details.
 |
| Figure 11. Screengrab of manual ORCID entry for co-authors to copy, 16 Feb 2026. |
By using the same DOI and handle.net address, we wanted to ensure that just one record was captured via ORCID for our paper (versus four separate records for all co-authors!).
A manual Academia.edu entry
Like ORCID, Academia.edu's manual field entries for an article support both the entry of the DOI value, and also related Links/URL (Figure 12). This contrasts to ResearchGate's support for just one DOI address.
 |
| Figure 12. Screenshot of adding handle.net entry to manual Academia.edu record, 16 Feb 2026. |
Cannot get (a) Kudos (addition)
Kudos is a networking platform designed to increase the visibility, reach, and impact of published research It supports scholars with explaining their work in plain language, and adding salient context. In theory, a DOI, article title or recent manual entry on ORCID should support Kudos with finding 'Brandjacked for social media advert fraud'. However, none of the three searches worked (Figure 13).
 |
| Figure 13. Screenshot of Kudos search options - DOI, text search & ORCID, 16 Feb 2026. |
I emailed Kudos' support team to flag this issue, asking if there was an alternate route for authors to add a publication. They replied that Kudos currently depends on the entry of DOIs: 'Please be aware that we do plan to create more options to add a publication to Kudos in the future and this is on our product roadmap. In the meantime we recommend that you kindly contact your publisher and ask them to send published work metadata to Crossref so it is more discoverable, and appears in Kudos and other online services' (email correspondence, 4 March, 2026),
Who is responsible for submitting to Crossref?
The primary responsibility for submitting and maintaining Crossref entries typically lies with the publisher in being formal Crossref members. CRIMSA publishes Acta Criminologica : African Journal of Criminology & Victimology. The editor ensures that high-quality metadata (such as ORCIDs and funding info) is received from authors before manuscript approval. CRIMSA would then be responsible for submitting accepted articles' bibliographic metadata (including URLs and references, plus registering DOIs), then ensuring this information remains up-to-date. The publisher handles the technical side of generating "Crossref XML" files, or using deposit tools.Like many small organisations though, CRIMSA's office bearers may be stretched across many roles. So, not able to prioritise learning how to do Crossref submissions as a new responsibility, let alone find the time to do them. The extra funds to pay for such work may also not be available.
In the near future, CRIMSA's academic journal does plan to submit metadata to Crossref for new articles. I have encouraged Acta Criminologica's editor to organise that its full archive becomes retroactively registered with Crossref. The estimated cost of $0.15 per article’s uploaded meta-data should hopefully not prove a showstopper. Supplying the correct metadata for all articles will benefit this journal's visibility, and hopefully support not just its altmetrics results being listed, but also Acta Criminologica being listed on journal portals used to rank and compare academic journals (and country-level scientific output). Notably, the free Scimagojr and Scilit portals.
Conclusion
After overcoming the challenges of review, revisions, and achieving a digital publication, academic authors may face a new challenge- following up that their publications are well-indexed. As this post illustrates, this must not be assumed. Rather authors must check that their article's DOI identifier does indeed link to their article's publication page. And that their paper's social media impact and amplification is being correctly reflected via that page's Altmetrics badge.
If there is a problem, it is most likely to be taking place in the earliest phase of the Research Data Lifecycle (RDLC)- this broad concept is used to describe the "cradle-to-grave" journey of research data:
In terms of sharing research outputs, it includes curation of metadata that is standardised, ensuring outputs are both disseminated, and findable via academic search engine optimisation (ASEO). And that the article's reach, amplification and media interest can be measured via Altmetric statistics.
In the case of our article, the DOI indexing flaw lay in phase 1 of output sharing. The journal does not supply metadata for its articles to the academic metadata aggregator, Crossref. Instead, the journal's publisher setup a temporary DOI as a workaround. While this may work as a stopgap measure, it poses a major obstacle for scholars keen to share the work with centralised registries in phase 2, since each co-author must manually create an ORCID record. In phase 3, academic aggregators (such as Google Scholar) may direct users to a 'page not found' response on doi.org or from the journal's website. In phase 4, researchers may face a similar problem on academic social networks (such as ResearchGate) which require an accurate DOI link. For phase 5, the ability of altmetrics services to track an article's amplification, reach and media interest is scuppered. By contrast, the article's citations are still tracked.
However, until this happens, authors keen to share their Acta Criminologica publications via their scholarly profiles and social networks must do a lot of extra work. My colleagues and I followed work-arounds to address the placeholder DOI index information in phases 2 to 4. These included listing their article's and/or handle.net address in manual entries on ORCID's centralised registry, academic aggregators (e.g. Google Scholar or Bielefeld Academic Search Engine). Plus, shifting to using the handle.net address in academic social network posts. These work-arounds required extra labour from the four authors, three of whom are independent and not formally affiliated to any university. As the journal publisher already covers the journal's Crossref fees, such extra work can readily be avoided. Hopefully, the journal will put aside the resources necessary for generating the required XML metadata, and for depositing its full archive, plus new publications via Crossref's record manager.
Related suggestions
Journal publishers and editorial teams can help their authors upfront by being transparent about what the opportunities and limitations of their journal's current indexing are in relation to sharing publications online. Plus, publishers should provide advice to authors for how these strengths and weaknesses support, or limit, the online visibility and potential amplification opportunities for their new works. For example, in Acta Criminologica : African Journal of Criminology & Victimology's case, it has several strengths, such as indexing works in the reputable databases of SABINET and African Journals OnLine (AJOL). However, its metadata is not currently submitted to Crossref, nor does the journal appear in Scopus title lists. As described regarding Crossref, this requires authors to make several work-arounds to ensure their articles become visible via centralised registries and academic aggregators. Authors must also accept that they cannot source altmetrics for their work, and cannot use services solely reliant on DOI link entries.
Publishers and editorial teams who provide transparency about their journals' academic indexing issues, could also make public their plans to resolve them. This would be performing a helpful service, not just for their authors, but also for potential case-study research in an area for which there seems to be a dearth of detailed local descriptions to learn from. With less than half of African journals being indexed in Crossref, there must be systemic problems preventing their indexing. Learning in detail from African journal publishers and editors on why this is the case, plus how it might be addressed on the ground, would seem a worthwhile gap for scholars to research, and close.
N.B. Kindly add a comment below if you have any related suggestions or other feedback...
Location: Cape Town, Western Cape Province, RSA
Cape Town, South Africa
Tuesday, 26 September 2023
Noteworthy disparities with four CAQDAS tools: explorations in organising live Twitter (now known as X) data
Written for researchers interested in extracting live X (formerly Twitter) data via Qualitative Data Analysis Software tools
QDAS tools that support live data extraction are a relatively recent innovation. At the time of our fieldwork, four prominent QDAS provided this: only ATLAS.ti™, NVivo™, MAXQDA™ and QDA Miner™ had Twitter data import functionalities. Little has been written concerning the research implications of differences between their functionalities, and how such disparities might contribute to contrasting analytical opportunities. Consequently, early-stage researchers may experience difficulties in choosing an apt QDAS to extract live data for Twitter academic research.
In response to both methodological gaps, we spent almost a year working on a software comparison to address the research question (RQ) 'How do QDAS packages differ in what they offer for live Twitter data research during the organisational stage of qualitative analysis?'. Comparing their possible disparities seems worthwhile since what QDAS cannot, or poorly, support may strongly impact researchers’ microblogging data, its organisation, and scholars’ potential findings. In the preliminary phase of research, we developed a features checklist for each package, based on their online manuals, product descriptions and forum feedback related to live Twitter imports. This checklist confirmed wide-ranging disparities between QDAS, which were not unexpected since they are priced very differently- ranging from $600 for an ATLAS.ti subscription, to $3,650 for a QDAMiner (as part of the Provalis Research’s ProSuite package, which also includes WordStat 10 & Simstat).
To ensure that each week's Twitter data extractions could produce much data for potential evaluation, we focused on extracting and organising communiqués from the national electrical company, the Electricity Supply Commission (Eskom). ‘Load-shedding’ is the Pan South African Language Board’s word of the year for 2022 (PanSALB, 2022), due to it most frequent use in credible print, broadcast and online media. Invented as a euphemism by Eskom’s public-relations team, load-shedding describes electricity blackouts. Since 2007, planned rolling blackouts have been used in a rotating schedule for periods ‘where short supply threatens the integrity of the grid’ (McGregor & Nuttall, 2013). In the weeks up to, and during, the researchers’ fieldwork, Eskom, and the different stages of loadshedding strongly trended on Twitter. These tweets reflected the depth of public disapproval, discontent, anger, frustration, and general concern.
QDAS packages commonly serve as tools that researchers can use for four broad activities in the qualitative analysis process (Gilbert, Jackson, & di Gregorio, 2014). These are (a) organising- coding sets, families and hyperlinking; (b) exploring - models, maps, networks, coding and text searches; (c) reflecting - through memoing, annotating and mapping; and (d) integrating qualitative data through memoing with hyperlinks and merging projects (Davidson & di Gregorio, 2011; Di Gregorio, 2010; Lewins & Silver, 2014).
To ensure that each week's Twitter data extractions could produce much data for potential evaluation, we focused on extracting and organising communiqués from the national electrical company, the Electricity Supply Commission (Eskom). ‘Load-shedding’ is the Pan South African Language Board’s word of the year for 2022 (PanSALB, 2022), due to it most frequent use in credible print, broadcast and online media. Invented as a euphemism by Eskom’s public-relations team, load-shedding describes electricity blackouts. Since 2007, planned rolling blackouts have been used in a rotating schedule for periods ‘where short supply threatens the integrity of the grid’ (McGregor & Nuttall, 2013). In the weeks up to, and during, the researchers’ fieldwork, Eskom, and the different stages of loadshedding strongly trended on Twitter. These tweets reflected the depth of public disapproval, discontent, anger, frustration, and general concern.
QDAS packages commonly serve as tools that researchers can use for four broad activities in the qualitative analysis process (Gilbert, Jackson, & di Gregorio, 2014). These are (a) organising- coding sets, families and hyperlinking; (b) exploring - models, maps, networks, coding and text searches; (c) reflecting - through memoing, annotating and mapping; and (d) integrating qualitative data through memoing with hyperlinks and merging projects (Davidson & di Gregorio, 2011; Di Gregorio, 2010; Lewins & Silver, 2014).
Notwithstanding the contrasts in the costs for different QDAS packages, it was still surprising how much the QDAS tools varied for the first activity, (a) ‘organising data’ in our qualitative research project: Notably, the quantum of data extracted for the same query differed, largely due to contrasts in the types and amount of data that the four QDAS could extract. Variations in how each supported visual organisation and thematic analysis also shaped researchers’ opportunities for becoming familiar with Twitter users and their tweet content.
Such disparities suggest that choosing a suitable QDAS for organising live Twitter data must dovetail with a researcher’s focus: ATLAS.ti accommodates scholars focused on wrangling unstructured data for personal meaning-making, while MAXQDA suits the mixed-methods researcher. QDA Miner’s easy-to-learn user interface suits a highly efficient implementation of methods, whilst NVivo supports relatively rapid analysis of tweet content.
We hope that these findings might help guide Twitter social science researchers and others in QDAS tool selection. Our research has suggested recommendations for these tools developers to follow for potentially improving the user experience for Twitter researchers. Future research might explore disparities in other qualitative research phases, or contrast data extraction routes for a variety of microblogging services. More broadly, an opportunity for a methodological contribution exists regarding research that can define a strong rationale for the software comparison method.
The authors greatly appreciate the SSRC's editor, Professor Stephen Lyon, advice on improving our final manuscript. We also thank The Noakes Foundation for its grant AFSDV02- our interdisciplinary software comparison would not have been possible without funding to cover subscriptions to the most extensive versions of MAXQDA Analytics Pro and QDA Miner. All authors are affiliated with the Cape Peninsula University of Technology (CPUT) and appreciate CPUT's provision of licensed versions of ATLAS.ti.
Please comment below if you have any questions or comments regarding our paper?
Please comment below if you have any questions or comments regarding our paper?
Labels:
academic
,
analysis
,
CAQDAS
,
QDAS
,
qualitative
,
research
,
social_network
,
software_comparison
,
Twitter
Location: Cape Town, Western Cape Province, RSA
Cape Town, South Africa
Friday, 23 December 2022
A summary of 'Who is watching the World Health Organisation? ‘Post-truth’ moments beyond infodemic research'
Written for infodemic/disinfodemic researchers and those interested in the scientific suppression of COVID-19 dissidents.
Dr David Bell, Emeritus Professor Tim Noakes and my opinion piece 'Who is watching the World Health Organisation? ‘Post-truth’ moments beyond infodemic research’ is available at https://td-sa.net/index.php/td/article/view/1263. It was written for a special issue, 'Fear and myth in a post-truth age’ from the Journal for Transdisciplinary Research in Southern Africa (see call at https://aosis.co.za/call-for-papers-special-collection-in-journal-for-transdisciplinary-research/).
A major criticism this paper raises is that infodemic research lacks earnest discussion on where health authorities’ own choices and guidelines might be contributing to ‘misinformation’, ‘disinformation’ and even ‘malinformation’. Rushed guidance based on weak evidence from international health organisations can perpetuate negative health and other societal outcomes, not ameliorate them! If health authorities’ choices are not up for review and debate, there is a danger that a hidden goal of the World Health Organisation (WHO) infodemic (or related disinfodemic funders’ research) could be to direct attention away from funders' multitude of failures in fighting pandemics with inappropriate guidelines and measures.
A major criticism this paper raises is that infodemic research lacks earnest discussion on where health authorities’ own choices and guidelines might be contributing to ‘misinformation’, ‘disinformation’ and even ‘malinformation’. Rushed guidance based on weak evidence from international health organisations can perpetuate negative health and other societal outcomes, not ameliorate them! If health authorities’ choices are not up for review and debate, there is a danger that a hidden goal of the World Health Organisation (WHO) infodemic (or related disinfodemic funders’ research) could be to direct attention away from funders' multitude of failures in fighting pandemics with inappropriate guidelines and measures.
In The regime of ‘post-truth’: COVID-19 and the politics of knowledge (at https://www.tandfonline.com/doi/abs/10.1080/01596306.2021.1965544), Kwok, Singh and Heimans (2019) describe how the global health crisis of COVID-19 presents a fertile ground for exploring the complex division of knowledge labour in a ‘post-truth’ era. Kwok et al. (2019) illustrates this by describing COVID-19 knowledge production at university. Our paper focuses on the relationships between health communication, public health policy and recommended medical interventions.
Divisions of knowledge labour are described for (1) the ‘infodemic/disinfodemic research agenda’, (2) ‘mRNA vaccine research’ and (3) ‘personal health responsibility’. We argue for exploring intra- and inter relationships between influential knowledge development fields. In particular, the vaccine manufacturing pharmaceutical companies that drive and promote mRNA knowledge production. Within divisions of knowledge labour (1-3), we identify key inter-group contradictions between the interests of agencies and their contrasting goals. Such conflicts are useful to consider in relation to potential gaps in the WHO’s infodemic research agenda:
For (1), a key contradiction is that infodemic scholars benefit from health authority funding may face difficulties questioning their “scientific” guidance. We flag how the WHO ’s advice for managing COVID-19 departed markedly from a 2019 review of evidence it commissioned (see https://www.ncbi.nlm.nih.gov/pubmed/35444988).
(2)’s division features very different contradictions. Notably, the pivotal role that pharmaceutical companies have in generating vaccine discourse is massively conflicted. Conflict of interest arises in pursuing costly research on novel mRNA vaccines because whether the company producing these therapies will ultimately benefit financially from the future sales of these therapies depends entirely on the published efficacy and safety results from their own research. The division of knowledge labour for (2) mRNA vaccine development should not be considered separately from COVID-19’s in Higher Education or the (1) infodemic research agenda. Multinational pharmaceutical companies direct the research agenda in academia and medical research discourse through the lucrative grants they distribute. Research organisations dependant on external funding for covering budget shortfalls will be more susceptible to the influence of those funders on their research programs.
However, from the perspective of orthodoxy, views that support new paradigms are unverified knowledge (and potentially "misinformation"). Any international health organisation that wishes to be an evaluator must have the scientific expertise for managing this ongoing ‘paradox’, or irresolvable contradiction. Organisations such as the WHO may theoretically be able to convene such knowledge, but their dependency on funding from conflicted parties would normally render them ineligible to perform such a task. This is particularly salient where powerful agents can collaborate across divisions of knowledge labour for establishing an institutional oligarchy. Such hegemonic collaboration can suppress alternative viewpoints that contest and query powerful agents’ interests.
It is concerning how many Communication and Media Studies researchers are ignoring such potential abuse of power, whilst supporting censorship of dissenters based on unproven "harms". Embedded researchers seem to ignore that the Centers for Disease Control, National Institute for Health and the WHO’s endorsement of multinational pharmaceutical companies’ products is a particularly troubling development: it marks a ‘new normal’ of institutional capture by industry sponsoring regulators who become their ‘lobbyists’. This contrasts to the silo efforts of external influence in the past, for example by lobbyists working for Big Tobacco or Big Food. They spun embedded scientific research touting the ‘benefits’ of smoking and processed foods. At the same time, evidence of harm was attacked as "junk science".
At least with cigarettes and ultra-processed foods, many individuals have the choice to buy or avoid paying. In stark contrast, tax-paying publics have no such option in avoiding the steep costs of mRNA vaccines. Public taxes pay for these treatments, while less expensive and potentially more effective interventions are ignored. Paying for vaccines takes funding away from interventions that would address wider and more pressing global health needs, in particular, poverty, malaria, tuberculosis and T2DM.
Our article results from collaboration between The Noakes Foundation and PANDA. The authors thank JTSA’s editors for the opportunity to contribute to its special issue, the paper’s critical reviewers for their helpful suggestions and AOSIS for editing and proof-reading the paper.
This is the third publication from The Noakes Foundation’s Academic Free Speech and Digital Voices (AFSDV) project. Do follow me on Twitter or https://www.researchgate.net/project/Academic-Free-Speech-and-Digital-Voices-AFSDV for updates regarding it.
I welcome you sharing constructive comments, below.
Labels:
academic
,
article
,
COVID-19
,
disinfodemic
,
infodemic
,
post-truth
,
research
Location: Cape Town, Western Cape Province, RSA
Cape Town, South Africa
Saturday, 23 April 2022
Eight conceptual challenges in developing the 'online academic bullying' framework
Written for scholars interested in understanding online harassment from academic cyberbullies, plus the development of the online academic bullying routine activity theory (OABRAT) framework
In developing our 'Distinguishing online academic bullying' article, Prof Tim Noakes and I trimmed the manuscript several times. Reworking some of these cuts in this post may offer value through addressing the methodological challenges we encountered in proposing our article's OABRAT framework. Seven conceptual challenges were overcome its development, while an eighth was encountered post-publication:
1 NEW FORMS OF POWER IMBALANCE
Conventional definitions of cyber-bullying suggest a power imbalance in which one aggressor is more powerful than his or her victim (Englander, Donnerstein, Kowalski, Lin, & Parti, 2017). By contrast, an established academic may be easily be targeted by individuals of varied statuses; who can mount frequent attacks as part of cybermobs. OAB differs from the conventional definition of cyberbullying in that there need not be a one-to-one power-imbalance in favour of the bully. It can include varied power relationships between a victim and his or her attackers: a standard power-imbalance may exist in the victim being on a lower rung of an academic cultural hierarchy within a particular field than the bullies (e.g. Cardiology has greater prestige than Sports Medicine in the medical field). However, a senior scholar may still be the subject of collegial mobbing (Davenport, Elliot and Schwartz, 1999). For example, the Emeritus Professor was attacked online by junior academics and non-scholars, from within his field and from other disciplines (see Figure 1 for his university).
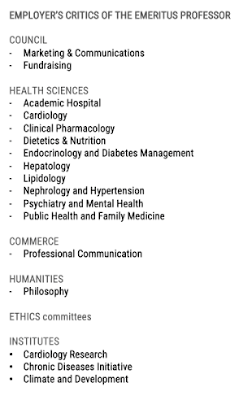 |
| Figure 1. Faculties and departments in which employees persistently criticised the Emeritus Professor on social media (Travis Noakes, 2020) |
Attacking a scientific dissident as a pre-defined target seemed to provide attackers with an instant form of credibility- they did not have to prove their symbolic credentials to gain visibility. Few of the professor's blogging critics were Health Science scholars. Despite making no scholarly contribution to the debate, some academic cyberbullies seemed to achieve visibility as opinion "leaders" online. This shows how micro-celebrity hijacking can apply for Higher Education (HE) employees. Academic bloggers criticise public intellectuals for "wrongthink" thereby gaining attentional capital- blogged critiques by "independent" critical thinkers can convert into appearances on broadcast media.
Power imbalances may also result from other differences in a victim’s status versus his or her attackers. These can span inequalities in capital (Bourdieu, 1986), notably social and cultural capital- a scholar who defends an unorthodox position is at a disadvantage in terms of her social capital. She will struggle to draw support against unfair criticism by organic groups of academic cyberbullies.
Another dimension of power imbalance may lie in technical cultural capital- an OAB recipient who has less knowledge of the digital platform(s) on which she is being attacked may be at a serious disadvantage. For example, cyberbullies can use advantages in their ‘digital dimensions’ (Paino & Renzulli, 2013) of cultural capital for gaining greater visibility. They can leverage a myriad of online presences for amplifying their attacks, whilst leveraging multiple chains of digital publication that are difficult for a victim to reply to.
This suggests another imbalance whereby OAB recipients will struggle to defend themselves against asymmetrical cyber-critiques. It may be exhausting to respond to frequent criticisms, across a myriad of digital platforms and conflicting timezones.
Another dimension of power imbalance may lie in technical cultural capital- an OAB recipient who has less knowledge of the digital platform(s) on which she is being attacked may be at a serious disadvantage. For example, cyberbullies can use advantages in their ‘digital dimensions’ (Paino & Renzulli, 2013) of cultural capital for gaining greater visibility. They can leverage a myriad of online presences for amplifying their attacks, whilst leveraging multiple chains of digital publication that are difficult for a victim to reply to.
This suggests another imbalance whereby OAB recipients will struggle to defend themselves against asymmetrical cyber-critiques. It may be exhausting to respond to frequent criticisms, across a myriad of digital platforms and conflicting timezones.
2 BEYOND TROLLS: ACADEMIC CYBERBULLIES AS DECEIVERS, FLAMERS, ETC.
Definitions of cyberbullying are in themselves broad, since
they may also cover electronic bullying and internet harassment (Berne et al., 2013) . Likewise, classifications for academic cyberbullies’ roles and behaviours must be wide-ranging to address how bullies can readily draw on many repertoires for anti-social communication. A highly agentive cyberbully could draw on practices that meet several characteristics- the mocking "jokes" of a malevolent troll, the swearing attacks of a 'flamer' and a 'deceiver''s misrepresentations in their self-presentation (e.g. a self-proclaimed "philosophe(r)"/"scholar" without a PhD). We chose not make sharp distinctions between an academic bully’s and
other online deviants' roles and behaviours, since this could actually include areas that strongly overlap. At the same time, we were mindful that defining OAB as a particular form of harassment by HE employees was important to ensure OAB does not become a catchall. There is a danger that definitions of harassment that are generalised can be misused in bad faith to apply to mere criticisms or mildly unpleasant language (Jeong, 2018).
3 SCIENTIFIC SUPPRESSION VERSUS BIO-MEDICAL HERESY "JUSTIFIES" HARASSMENT
When a challenger to orthodoxy begins to attract attention from patients, the general public and the press, then those in power will take active steps to protect the reigning paradigms (Martin, 2004). Adherents to the dominant ideology will view such individuals' questioning of the central values of their CMCDD orthodoxy as performing heresy. Heresy is created by the response of the orthodoxy when its views' delineate attacks as beyond the pale (Wolpe, 1994). Defenders of CMCDD might justify their harassment in believing that only high carbohydrate/low fat diets are “healthy”. Followers of this belief have argued that pursuing any other ideas or approaches constitute a "threat to public health". Following this rationale, such critics may argue for censorship of dissidents' "dangerous" work and to limit digital publics' exposure to state-of-the-art IRMCIH science news.
Defenders of the status-quo enjoy visibility as part of dominant networks and can readily spotlight “heretics” for criticism via formal and informal channels, such as social media. Recipients must negotiate rapidly-spreading disinformation, defamation, misrepresentation-of-argument and even character assassination HE employees involved in such adverse actions typically explain their actions as being justified in maintaining 'academic standards'' (Martin, 2020). However, such actions are detrimental in silencing dissenters' and whistleblowers' free speech, thereby stifling scientific debate and potential innovations.
4 FOREGROUNDING THE VICTIM’S PERSPECTIVE
5 ACADEMIC CYBERMOBBING- SEPARATE FROM AN ACADEMIC MOB
The Emeritus Professor's case study was closely linked to a formal mobbing at his former academic institutional employer. In the initial manuscript, we foregrounded this strong overlap: His employer's neglect of rules and policies against harassment by its employees provides a fertile space for harassment (Benatar, 2021). Senior leaders followed a dominating conflict culture (DCC) approach (Desrayaud et al., 2018) in protecting the Faculty of Health Science's (FHS) CMCDD orthodoxy from criticism. Although DCC actively encourages discourse about incompatible goals and ideas, DCC does not acknowledge the validity of opposing views. In a toxic DCC workplace, dissent is ignored and support for dissenters is withheld. Explicit bullying is seen as an acceptable response to intellectual differences and overt mobbing is also condoned. In this respect, attacks on the Emeritus Professor were similar to the bullying of other senior scholars that university leadership clearly tolerated (Benatar, 2017; Coovadia, 2015; Crowe, 2017; Crowe, 2019; McCain, 2020; Plaut, 2020; Soudien, 2015; Steer, 2019; Vernac News, 2019). In 2019, his employer's institution acknowledged that bullying was a major concern amongst staff (Feris, 2019), but has yet to recognise the importance of addressing DCC in its FHS. One positive recent development is that an anti-bullying policy was passed (2021). Albeit, a very late response to its former Ombudsman's recommendation from 2012 (Makamandela-Mguqulwa, 2020).
In university workplaces, bullies can use a justification of “academic freedom” to condone actions that would be unacceptable in other workplaces (Driver, 2018). For example, an academic lecturer (who is neither a scholar nor a scientist) published thirty blog posts that criticised the Emeritus Professor's popularisation of LCHF science. Although by no means an academic peer, this junior lecturer might justify such fervent criticism of a fellow employee at the same university as a necessary part of academic freedom in an institute of higher learning. Nevertheless, such obsessive behaviour from a low-ranking, under-qualified employee seems unlikely to be acceptable at any other place of employment.
In collating the varied forms of harassment from "academic colleagues", it was unsurprising that we initially considered a recipient's OAB as being inseparable from an experience of academic mobbing in the HE context. However, the manuscript's reviewers flagged that it could be separate- especially for targets outside HE. In response, we designed the OABRAT framework to accommodate a separate phenomenon.
Such separation also addressed concerns that the private, departmental ostracisation of ‘academic mobbing’ in HE (Seguin, 2016. Khoo, 2010) is a very different negative phenomenon from the public attacks that academic cyberbullies launch. Unlike the largely concealed backstabbing of an academic mob, academic cyberbullies criticisms are public. OAB recipients can readily spot critics and their networks in digital criticisms, such as group petitions. Like others cybermobbers, public attacks fall within a spectrum that can include: i. drive-by harassment, ii. low-level mobbing, iii. sustained hounding and iv. sustained orchestration (Jeong, 2018). Professor Noakes and I are working on a manuscript that explores this spectrum for defining an ‘academic cybermobbing’'s particular characteristics.
6 GUARDIANS AGAINST VICTIMS OF ACADEMIC BULLYING
In addition to considering academic cyberbullies practices and their recipients experiences, it is also vital to address the role of guardians. RAT supports addressing the activities of both the targets of crime, plus their guardians. In academic cyberbullying, it is important to consider how the online activities of a victim could be placing him or her at added risk. It is also worthwhile considering how the lack of action from guardians of civility, whether they be at the scholar’s academic institution or moderators for social media platforms, has an impact. Prevention would seem better than cure for the negative phenomenon of persistent cyber harassment. In OAB, this emerges when a large quantum of criticism from academic cyberbullies creates an easily searchable footprint.
Policies protecting employees at HE institutes from workplace persecution have largely focused on sexual and racial harassment. The danger exists that other forms of persecution may be neglected as seeming relatively unimportant by comparison (Citron, 2007). For example, aggressive behaviours in the workplace may be considered acceptable by default (Rayner, Hoel, & Cooper, 2002). Informal expectations and norms can increase the sense of a lack of accountability online and boost the likelihood of deviant behaviours. Without deterrents or any consequences for academic cyberbullying, bullies may believe that they will not be held accountable for their actions. Worse, hegemonic leadership may actually reward those whose cyberbullying seems to maintain perceptions of consensus. In HE, such rewards are unethical in undermining academic free speech, scientific innovation and motivating academic cyberbullying.
7 ACADEMIC BULLIES MAY TARGET OUTSIDERS FROM ANYWHERE
In conceptualising OAB, we came to argue that the victims of academic cyberbullies need not be HE employees. Feedback from IRMCIH proponents in varied health professions, plus LCHF entrepreneurs, confirmed attacks from cyberbullies in HE. While our literature review produced many examples of dissenting scientists and academic whistleblowers being confronted academic mobs, there is a gap concerning cases for bullying victims outside HE. This is another area that The Noakes Foundation's Academic Free Speech and Digital Voices (AFSDV) project can address for the IRMCIH scientific issue arena.
After Professor Noakes and I submitted the article for publication, we identified another concern to explore under the AFSDV theme:
8 A COMPLEX FORM FOR AN EXTREME CASE
GRAPHIC CREDITS
Stop, academic bully! shushmoji™ graphics courtesy of Create With Cape Town.
Labels:
academic
,
bullying
,
cyberbullying
,
higher education
,
research
Location: Cape Town, Western Cape Province, RSA
Cape Town, South Africa
Subscribe to:
Comments
(
Atom
)









 orcid.org/0000-0001-9566-8983
orcid.org/0000-0001-9566-8983
